A backup is only as good as your ability to recover from it — fast.
Picture this: a midsize client gets hit by a ransomware attack. Attackers lock systems, encrypt critical files and paralyze productivity. The only path forward is a fast, clean recovery from backup. However, when it’s time to act, recovery fails because the backup was never tested. Or worse, the backup is infected too. Now the client is stuck, the ransom clock is ticking and the MSP is left answering tough questions.
This is why “we have backups” has stopped being a reassuring response.
In today’s threat and regulatory landscape, backups that exist aren’t the same as backups that work. As cyberattacks become more advanced and compliance pressures rise, MSPs can no longer rely on traditional backup strategies that do not guarantee operational continuity and swift recovery. Clients need uninterrupted operations. They need visibility into what’s working and what isn’t. More importantly, they need assurance.
That’s why more MSPs are moving beyond traditional backup strategies to embrace a mature cyber resilience model. Below, we’ll explore why this shift matters, the three stages of cyber resilience maturity and how verified recovery and compliance readiness form the foundation of that evolution. Let’s see how MSPs can achieve predictable, profitable service delivery in a world where risks are higher and client expectations keep rising.
Why backup alone falls short of today’s client, regulatory and insurance demands
Client expectations have changed. They now require faster SLAs, clear recovery timelines and documented proof that systems can be restored after an incident. This has raised the bar for MSPs. Simply having a backup is no longer enough to meet these demands or deliver the level of confidence clients expect.
A completed backup job doesn’t guarantee a successful recovery. It doesn’t confirm data integrity. It doesn’t prove that systems will be restored within the SLA. For clients, this uncertainty can translate into extended downtime, financial loss and reputational damage.
And it’s not just clients applying pressure. Regulators and cyber insurers are now demanding hard evidence of cyber resilience. Insurance underwriters increasingly request documentation showing backup and recovery testing has been performed. Regulatory bodies expect MSPs to prove alignment with compliance frameworks. When backup and recovery success can’t be verified, the risk becomes more than technical — it becomes legal, financial and reputational.
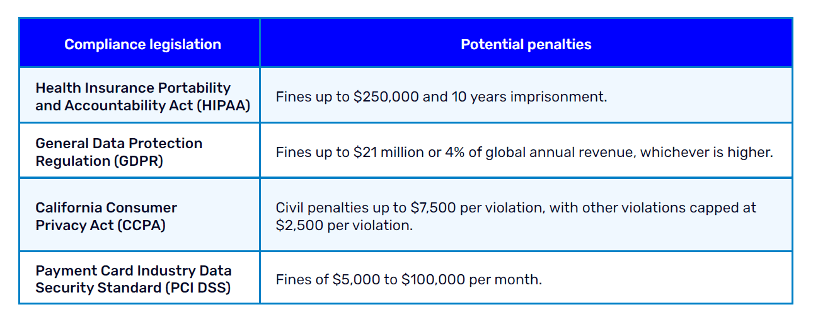
Fig 1: Some compliance legislations and potential penalties
The hidden cost of unverified backup and recovery in large-scale MSP operations
For MSPs managing multiple clients across complex environments, unverified backup and recovery introduces daily friction.
As environments expand across on-prem, cloud and hybrid infrastructure, tracking backup health becomes increasingly difficult. Visibility breaks down across systems, locations and clients. At the same time, recovery outcomes remain inconsistent. Failures often surface only during live incidents, when time pressure is highest and the impact is greatest.
Without automation, technicians spend hours manually checking backup jobs and troubleshooting issues after the fact. Reporting remains fragmented, making it harder to demonstrate resilience, support audits or standardize onboarding for new clients. Each new environment adds operational overhead instead of efficiency.
Without verification, every backup becomes a risk, and every recovery becomes a gamble. For MSPs focused on growth, efficiency and resilience, this model simply doesn’t scale.
Moving from backup to business assurance: The cyber resilience maturity curve
High-growth MSPs are shifting the way they think about cyber resilience, making it a measurable business capability that supports operational scale, client trust and long-term growth.
This evolution follows a clear maturity curve:
- Stage 1 – Backup-focused: Simply backing up data
- Stage 2 – Recovery-centric: Proving recoverability, but without assurance
- Stage 3 – Assurance-led: Delivering cyber resilience at scale
Stage 1 – Backup-focused: Data is backed up, but recovery isn’t guaranteed
This is where most MSPs begin — and where many remain. Backups run across client environments, whether on-prem, cloud or hybrid, but success is measured by job completion, not recovery.
Key traits:
- Manual or limited testing
- Minimal visibility into backup integrity
- No centralized reporting or trend analysis
- Backup failures go unnoticed until recovery is needed
- Inconsistent backup schedules across clients
Consequences:
- Recovery failures during incidents
- Missed recovery time objective (RTO)/recovery point objective (RPO) targets
- Inability to prove resilience during audits
- Technicians forced into reactive troubleshooting
- Higher client churn from avoidable downtime
Backup alone creates a false sense of security. Without visibility or validation, MSPs are left hoping their backups work — and hope is not a strategy.
Stage 2 – Recovery-centric: Recovery improves, but scale breaks
At this stage, MSPs shift from asking “Is it backed up?” to “Can we recover it?” Recovery confidence improves, and incident-time surprises start to decline.
What improves:
- Fewer failed recoveries
- Faster incident resolution
- A stronger SLA foundation
Challenges persist:
- Manual, inconsistent testing
- High technician effort
- Fragmented reporting
- Poor repeatability across clients
The core issue is repeatability here. Recovery exists, but it’s not predictable, provable or efficient at scale. As MSPs grow, these gaps become harder to ignore.
Stage 3 – Assurance-led: Cyber resilience becomes a scalable business capability
This is where cyber resilience becomes a business driver. Recovery isn’t just possible; it’s proven. Compliance isn’t reactive; it’s built in. MSPs at this stage can deliver consistent, audit-ready assurance across every client, location and workload.
Key traits:
- Automated, continuous backup and recovery validation
- Embedded compliance readiness
- Visibility across technical and business teams
What changes:
- Reactive protection becomes proactive assurance
- Resilience is standardized and reportable
- MSPs commit to outcomes with confidence
This is where resilience becomes predictable, provable and monetizable. It allows MSPs to scale services, enter regulated markets and support long-term growth without compromising service quality or operational efficiency.
The two pillars of a mature cyber resilience model: Verified recovery and compliance readiness
Verified recovery and compliance readiness are the foundation of an assurance-led cyber resilience model.
- Verified recovery ensures every workload is backed up and can be restored — with proof, not assumptions.
- Compliance readiness embeds regulatory alignment into daily operations, making audits easier and meeting rising client and industry expectations.
Together, they help MSPs meet SLAs, reduce risk, operate efficiently at scale and deliver premium cyber resilience services.
Verified recovery: From assumed protection to proven outcomes
Verified recovery is a capability MSPs need to build to move beyond assumptions and deliver backup and recovery confidence at scale. It replaces manual testing with automated validation of backup and recovery across clients and environments, ensuring recovery works when it matters most.
To make this possible, MSPs need to adopt key recovery capabilities, including:
- Instant virtualization to bring client systems online quickly across on-prem, cloud or hybrid infrastructure, minimizing downtime during recovery.
- Screenshot verification to confirm that backups boot and restore successfully, providing visual proof of recoverability.
- Application verification to ensure critical services like SQL, DHCP, Active Directory and DNS start and function properly after recovery.
- Service verification to confirm that system-level services — such as security configurations, network settings and remote access — are operational upon boot.
- Ransomware detection to alert IT teams to suspicious activity before it spreads to backup infrastructure, protecting recovery integrity.
Building these capabilities allows MSPs to reduce technician workload, meet SLAs with confidence and scale recovery operations across a growing client base.
Compliance readiness: Turning resilience into trust and differentiation
To compete and grow in today’s market, MSPs have to do more than deliver uptime — they must deliver compliance. Building a compliance-ready portfolio is the key to earning trust, expanding into regulated sectors and delivering resilience that stands up to scrutiny.
MSPs that want to serve regulated industries, such as government, healthcare, finance or education, need to weave compliance into every aspect of their cyber resilience offering. That includes implementing end-to-end cryptographic protection, validated to standards such as FIPS 140-3, across backup, recovery and virtualization workflows — not just during storage, but in transit and during active use.
They must also account for region- and industry-specific compliance requirements, especially when managing SaaS workloads on platforms such as Microsoft 365 and Google Workspace. Regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) and the General Data Protection Regulation (GDPR), often mandate strict retention policies, access controls and audit trails. For example, healthcare providers may require multi-year retention with auditable access logs, while financial clients may need immutable backups and fast eDiscovery support. MSPs should be mindful of these varying requirements to ensure their services stay compliant, scalable and trusted across industries.
Embedding compliance into the fabric of service delivery helps MSPs:
- Build trust with enterprise clients and compliance officers.
- Reduce audit and vendor assessment risks.
- Expand into higher-value, regulated markets with confidence.
- Align with the policies, standards and expectations of every client.
Cyber resilience that’s proven, repeatable and profitable
A mature cyber resilience strategy does more than protect data. It drives operational efficiency, strengthens client retention and builds long-term business value. By embedding verified recovery and compliance readiness into their service portfolio, MSPs can unlock new growth opportunities, protect margins and scale with confidence in a competitive market.
Ready to take it a step further? Want proven tips to sell business continuity and disaster recovery services more effectively? Download the checklist: BCDR sales made MSPeasy: 10 proven tips for winning clients.