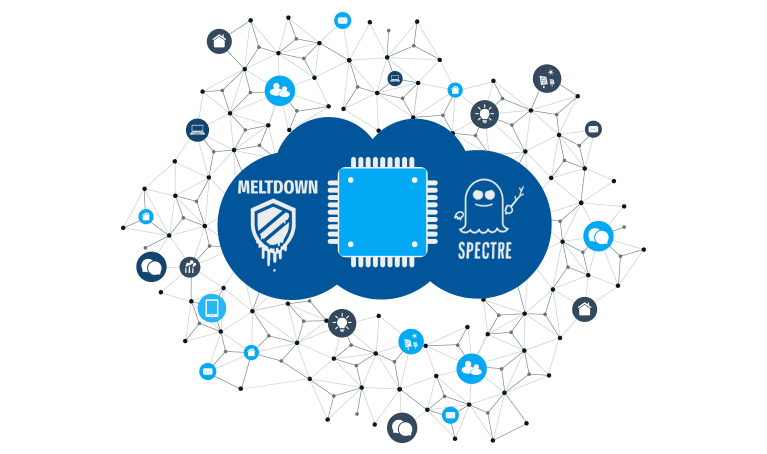
What is Meltdown & Spectre?
Meltdown and Spectre are similar in that they exploit newly found vulnerabilities in popular processors from Intel and AMD. The potential is that hackers can take advantage of these hardware vulnerabilities to devise attacks that steal data from and across applications. This includes passwords, private documents, contacts, and even financial information.
What's the Difference

Meltdown can exploit vulnerabilities in all Intel CPUs going back to 1995, adding up to hundreds of millions of devices. Meltdown can obtain information by “snooping” on memory used by the kernel.
Spectre can impact all three major processor families, Intel, AMD, and ARM. Using “speculative execution” this proof of concept exploit can steal forward-looking data held in the cache.
What's the Impact?
Every Intel processor which implements out-of-order execution is potentially affected by Meltdown, which is effectively every processor since 1995. Currently, It’s only verified Meltdown on Intel processors. At the moment, it is unclear whether ARM and AMD processors are also affected by Meltdown. Spectre impacts all modern processors, including intel, ARM, and AMD.
Meltdown & Spectre Resources

Download the Spectre Vulnerability Check
Learn More
Stay Up to Date with Our Meltdown and Spectre Knowledgebase
Learn More