Download Your White Paper Now
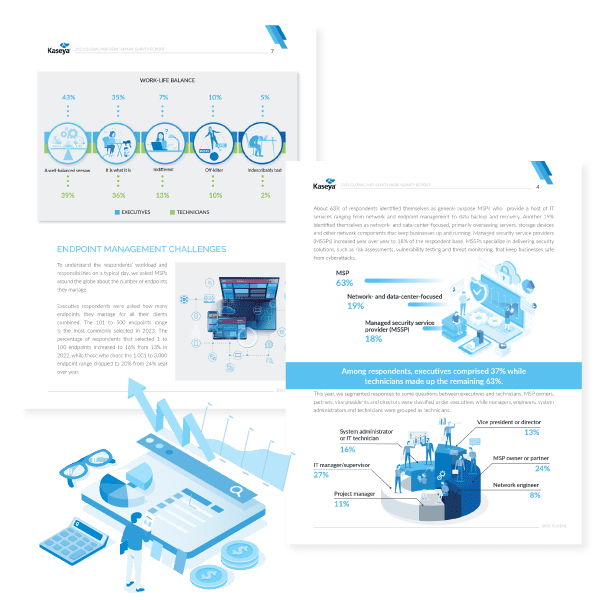
The events of the last few years have ushered in significant changes in how businesses worldwide conduct their business, and the MSP industry has been at the center of it. This year, MSPs will face recessionary winds, fierce competition and technology changes that will shape how they work going forward. The MSP Benchmark Survey Report 2023 highlights the changes taking place in the industry and how the MSPs are responding to them.
Download this report to get industry insights and statistics to help you make better decisions, navigate an uncertain economic environment and spot opportunities ahead. You’ll find information on automation, integration, MSP challenges, growth plans and more.

